For Companies
Security of Information Management
Implementation of an information security management system in accordance with relevant standards, consulting and auditor services.
CISO Services
Thanks to the external assurance of the position of Chief Information Security Officer, the IS security solution is more accessible.
eDiscovery and Forensic Analysis
In the event of an imminent or past security incident, it is necessary to analyze its extent and causes.
Forensic Report
Elaboration of a forensic report in the field of information and communication technologies and information security.
Sale and Rental of HW and SW
Sale or rental of specialized HW and SW for forensic data security and their subsequent analysis and reporting.
Data Recovery
Data recovery from damaged storage devices - hard drives, USB flash drives, memory cards or phones.
Secure Data Erasing
Reliable erasing of data from storage media comes in handy especially when selling a disk or a computer.
Training
We offer a wide range of training in the field of IT security for professionals in organizations and ordinary employees.
For Individuals
Forensic Report
Elaboration of a forensic report in the field of information and communication technologies and information security.
Data Recovery
Data recovery from damaged storage devices - hard drives, USB flash drives, memory cards or phones.
Secure Data Erasing
Reliable erasing of data from storage media comes in handy especially when selling a disk or a computer.
Computer and Telephone Security
We will help you with the appropriate settings for the security of your data in accordance with individual risks.
From our Blog (Czech)
Dvoufaktorová autentizace
Většina lidí v dnešní době má svá data nějak chráněna – nejčastěji heslem. Avšak i poměrně složité heslo může být různými způsoby prolomeno, takže přichází na řadu další stupeň ochrany: dvoufaktorová autentizace (česky dvoufaktorové ověření). V tomto...
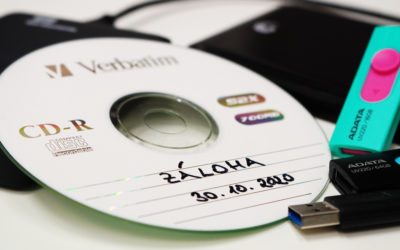
Zálohování dat
Říká se, že jsou dva typy lidí: ti, kteří si data zálohují a ti, kteří ještě o žádná nepřišli. Zálohování by mělo být pojistkou v případě, že jste o svá data z nějakého důvodu přišli a potřebujete je obnovit. Proto je...
Bezpečnost hesel
V dnešním světě má skoro každý svá data chráněna nějakým heslem (a kdo nemá, měl by to rychle napravit). Ovšem pouhé vytvoření a používání hesla není samospásné, je důležité znát bezpečnost hesel, možnosti prolomení a především jak vytvořit silné a bezpečné heslo....